Email remains the most critical business communication channel. Contracts, invoices, password resets, marketing campaigns, and compliance notifications all depend on reliable message delivery. Yet many organizations overlook the technical layer that ensures those messages reach their destination securely. If you want to define yourself as a trustworthy digital business, you must understand how your email infrastructure operates and how it can be abused. Simple Mail Transfer Protocol (SMTP) is the foundation of that infrastructure.
Table of contents
- What Is SMTP?
- How SMTP Works in Practice
- Why SMTP Configuration Defines Business Reputation
- SMTP Ports and Encryption Explained
- SMTP vs IMAP vs POP3
- Security Risks Associated with SMTP
- Strengthening SMTP Security
- The Overlooked Risk: Web Forms and SMTP Abuse
- Future Outlook for SMTP Security
- Conclusion
- FAQ – Frequently Asked Questions
What Is SMTP?
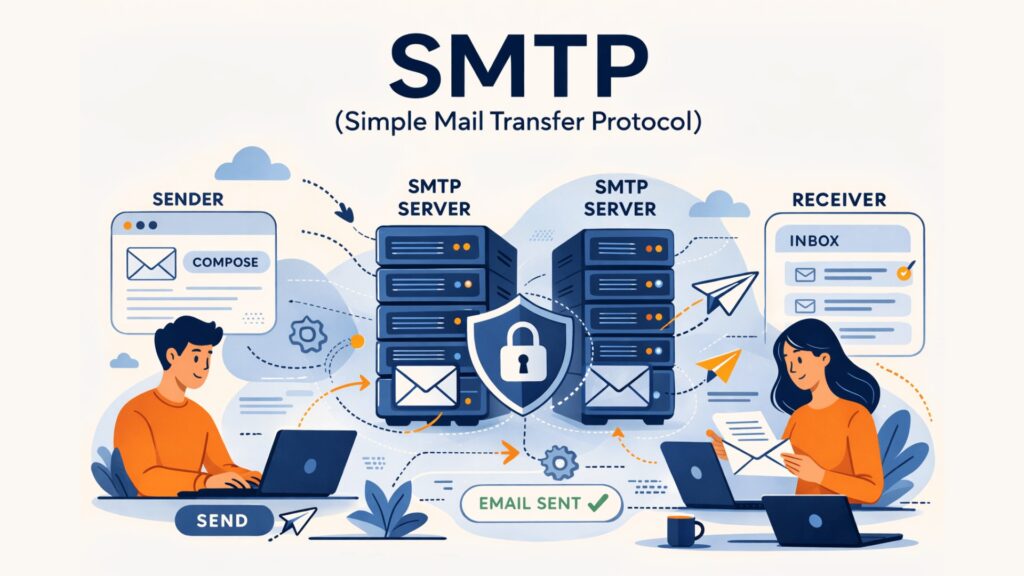
Simple Mail Transfer Protocol is the standard internet protocol used to send and relay email messages between servers. It defines how mail servers communicate, transfer message data, and confirm successful delivery across networks.
SMTP operates at the application layer of the Internet Protocol suite. It handles outgoing email traffic. When you send a message, SMTP pushes it from your email client to your mail server and then forwards it to the recipient’s mail server. Other protocols such as IMAP or POP3 retrieve messages from the inbox. SMTP focuses solely on sending and relaying. This distinction is critical for both technical teams and decision-makers who need clarity about responsibility within email systems.
How SMTP Works in Practice
SMTP follows a structured client-server communication model. When a user sends an email, the client opens a TCP connection to the outgoing mail server. The server responds and identifies itself. The sender’s server initiates a handshake using commands such as EHLO. It then specifies the sender and recipient addresses using MAIL FROM and RCPT TO instructions. Once accepted, the DATA command transmits the message body, headers, and attachments.
After receiving the message, the sending server queries the Domain Name System (DNS) to locate the recipient’s mail server via MX records. The message is relayed through one or more servers until it reaches the destination. This entire process occurs within seconds. However, each stage introduces potential security risks if misconfigured.
Why SMTP Configuration Defines Business Reputation
Major providers such as Google publish clear sender requirements through their Google Email Sender Guidelines, which directly influence deliverability. If your SMTP configuration lacks authentication or encryption, receiving servers may reject or flag your messages as suspicious.
Proper SMTP configuration allows you to define yourself as a legitimate sender. High deliverability ensures that invoices reach customers and password reset links function reliably. Poor configuration leads to blacklisting, spam filtering and long-term damage to your IP reputation.
Marketing teams feel the impact immediately. A blocked campaign reduces revenue. Transactional email failures disrupt customer experience. In regulated industries, delivery failures may even create compliance risks. SMTP infrastructure therefore influences revenue, brand credibility, and regulatory posture simultaneously.
SMTP Ports and Encryption Explained
Simple Mail Transfer Protocol relies on designated network ports defined by the Internet Assigned Numbers Authority (IANA). Port 25 traditionally handles server-to-server relay. Many providers restrict it due to spam abuse. Port 587 is the modern standard for email submission. It supports STARTTLS, which upgrades the connection to encrypted communication. Port 465 supports implicit TLS encryption, though historical inconsistencies exist in its usage.
Encryption matters. Without TLS, SMTP transmits data in plain text. Attackers monitoring network traffic could intercept credentials or message contents. Enforcing TLS 1.2 or higher protects data in transit and supports regulatory obligations such as GDPR data protection requirements. Encryption does not solve all risks, but it removes a critical vulnerability in transit.
SMTP vs IMAP vs POP3
Confusion between sending and receiving protocols is common. SMTP sends messages. IMAP and POP3 retrieve them.
IMAP synchronizes messages across devices and keeps mail stored on the server. POP3 downloads messages locally and often removes them from the server afterward. Businesses typically prefer IMAP for multi-device environments.
Understanding this distinction prevents misdiagnosis when delivery problems occur. If an email fails to send, the issue often lies in SMTP configuration. If it fails to appear in the inbox, retrieval protocols or filtering rules may be responsible. Clarity here reduces troubleshooting time and operational friction.
Security Risks Associated with SMTP
SMTP was originally designed without strong built-in authentication. Modern extensions improve security, but misconfigurations remain common. Open relays are one example. An improperly configured SMTP server may allow anyone to send messages through it. Attackers exploit this to distribute spam or phishing campaigns, quickly leading to blacklisting.
Email spoofing is another major risk. Attackers manipulate SMTP headers to impersonate executives or trusted vendors. This enables Business Email Compromise attacks that cause significant financial losses.
STARTTLS downgrade attacks represent a more technical threat. An attacker intercepts the handshake and prevents encryption from activating, forcing plain-text transmission. Without strict TLS enforcement, sensitive data may leak. These risks demonstrate why SMTP configuration cannot remain an afterthought.
Strengthening SMTP Security
European cybersecurity authorities such as ENISA recommend layered email security controls to prevent spoofing and abuse. Authentication frameworks such as SPF, DKIM, and DMARC validate sender identity. SPF defines authorized sending servers. DKIM adds cryptographic signatures to messages. DMARC instructs receiving servers how to handle authentication failures.
Strong credentials and restricted relay permissions prevent unauthorized use. Monitoring bounce rates and abnormal sending patterns helps detect compromised accounts early.
Transport security should enforce modern TLS versions and disable outdated protocols. Logging and audit trails support forensic analysis in case of incidents. SMTP security requires both technical controls and operational oversight.
The Overlooked Risk: Web Forms and SMTP Abuse
Many SMTP abuses begin at web forms. Contact forms, registration pages, and password reset workflows trigger outbound email. Bots frequently exploit these endpoints to send spam or test stolen credentials.
Even a perfectly configured SMTP server cannot prevent abuse if automated scripts generate large volumes of requests. Infrastructure-level security must extend to the application layer.
captcha.eu supports this layer by distinguishing legitimate users from automated bots before form submissions trigger SMTP processes. As a GDPR-compliant provider based in Austria, captcha.eu enables organizations to protect their email infrastructure while maintaining European data protection standards. This layered approach aligns infrastructure security with privacy compliance.
Future Outlook for SMTP Security
Email providers continue tightening authentication requirements. Major inbox platforms increasingly reject unauthenticated bulk mail. AI-driven filtering systems analyze behavioral signals in addition to protocol-level checks.
Zero-trust principles are also influencing email infrastructure. Organizations treat internal email traffic with the same scrutiny as external communication.
As digital communication grows more regulated, SMTP compliance and monitoring will become baseline requirements rather than optional improvements. Organizations that define themselves through secure, authenticated communication will maintain stronger deliverability and resilience.
Conclusion
SMTP forms the backbone of digital communication. It governs how email travels across the internet and directly affects deliverability, reputation, and security. Misconfiguration exposes organizations to spoofing, blacklisting, and regulatory risk. Proper configuration strengthens trust and operational reliability.
However, SMTP security extends beyond server configuration. Web entry points must also be protected against automated abuse. captcha.eu complements secure SMTP deployment by preventing bot-driven form exploitation while maintaining GDPR compliance.
To define yourself as a secure and trustworthy organization, you must secure both the transport protocol and the interaction points that trigger it.
FAQ – Frequently Asked Questions
What is SMTP used for?
SMTP is used to send and relay email messages between servers across the internet.
Is SMTP secure by default?
No. Basic SMTP transmits data in plain text. Security requires TLS encryption and authentication protocols such as SPF, DKIM, and DMARC.
What port should SMTP use?
Port 587 with STARTTLS is the recommended standard for secure email submission.
What is the difference between SMTP and IMAP?
SMTP sends email messages, while IMAP retrieves and synchronizes them across devices.
Can SMTP be abused by bots?
Yes. Bots can exploit web forms or misconfigured servers to send spam or phishing messages.
100 free requests
You have the opportunity to test and try our product with 100 free requests.
If you have any questions
Contact us
Our support team is available to assist you.




